What is SettingSyncHost.exe?
SettingSyncHost.exe is an executable exe file which belongs to the Host Process for Setting Synchronization process which comes along with the Microsoft Windows Operating System Software developed by Microsoft Windows Operating System software developer.
If the SettingSyncHost.exe process running in the Windows Operating system is important, then you should be careful while deleting it. Sometimes SettingSyncHost.exe process might be using CPU or GPU too much. If it is malware or a virus, it might be running in the background without you knowing it.
The .exe extension of the SettingSyncHost.exe file specifies that it is an executable file for Windows Operating Systems like Windows XP, Windows 7, Windows 8, and Windows 10.
Malware and viruses are also transmitted through exe files. So we must be sure before running any unknown executable file on our computers or laptops.
Now we will check if the SettingSyncHost.exe file is a virus or malware. Whether it should be deleted to keep your computer safe? Read more below.
Is SettingSyncHost.exe safe to run? Is it a virus or malware?
Let’s check the location of this exe file to determine whether this is legit software or a virus. The location of this file and dangerous rating is.
File Location / Rating: 1% dangerous
To check whether the exe file is legit you can start the Task Manager. Then click on the columns field and add Verified Signer as one of the columns.
Now, look at the Verified Signer value for SettingSyncHost.exe process if it says “Unable to verify” then the file may be a virus.
| File Name | SettingSyncHost.exe |
| Software Developer | Microsoft Windows Operating System |
| File Type | EXE |
| File Location | 1% dangerous |
| Software | Microsoft Windows Operating System |
Over All Ratings for SettingSyncHost.exe : 4/5
Next, check the developer of SettingSyncHost.exe. If the developer of the software is legitimate, then it is not a virus or malware. If the developer is not listed or seems suspicious, you can remove it using the uninstall program.
Based on our analysis, we have displayed our result of whether this SettingSyncHost file is a virus or malware below.
Is SettingSyncHost.exe A Virus or Malware: SettingSyncHost.exe is not a Virus.
How to check if SettingSyncHost.exe is a security issue?
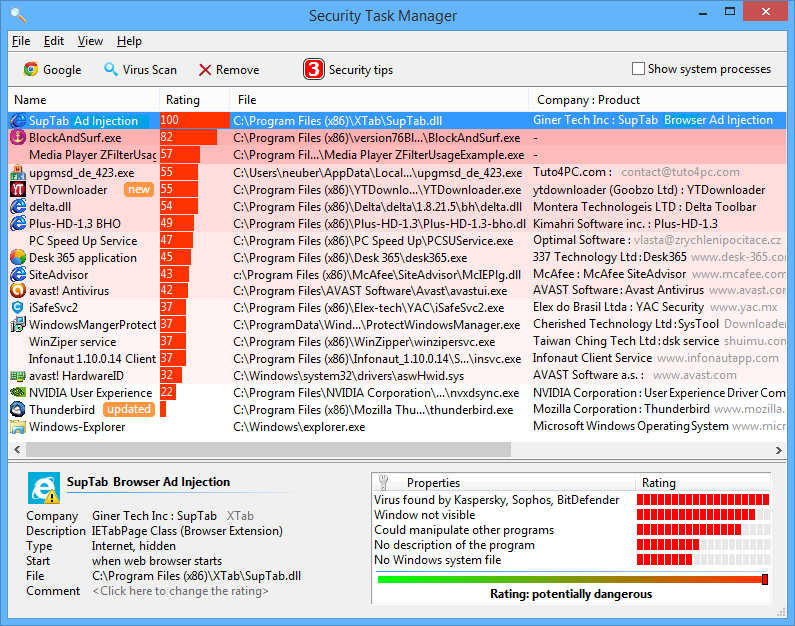
We also recommend using the Security task manager application to find which processes are unwanted in your Windows computer and can be a security issue. Here is how you can find whether SettingSyncHost.exe is a security threat using the Security Task Manager application.
- Download the Security Task Manager application and install it on your computer.
- Run it as administrator. It will now show all the applications that are running on your computer.
- Now it will show the Rating, file location, company, and product name for each process.
- Now click on the rating column to sort based on ratings.
- You will now see which process has the worst rating easily so can decide SettingSyncHost.exe is given a bad rating or not easily.
- You will also find whether the SettingSyncHost.exe process is important or not with this feature. Here is a screenshot of the software running on our windows computer.
How To Remove or Uninstall SettingSyncHost.exe
To remove SettingSyncHost.exe from your computer do the following steps one by one. This will uninstall SettingSyncHost.exe if it was part of the software installed on your computer.
- If the file is part of a software program, then it will also have an uninstall program. Then you can run the Uninstaller located at directory like C:Program Files>Microsoft Windows Operating System>Microsoft Windows Operating System >Host Process for Setting Synchronization> SettingSyncHost.exe_uninstall.exe.
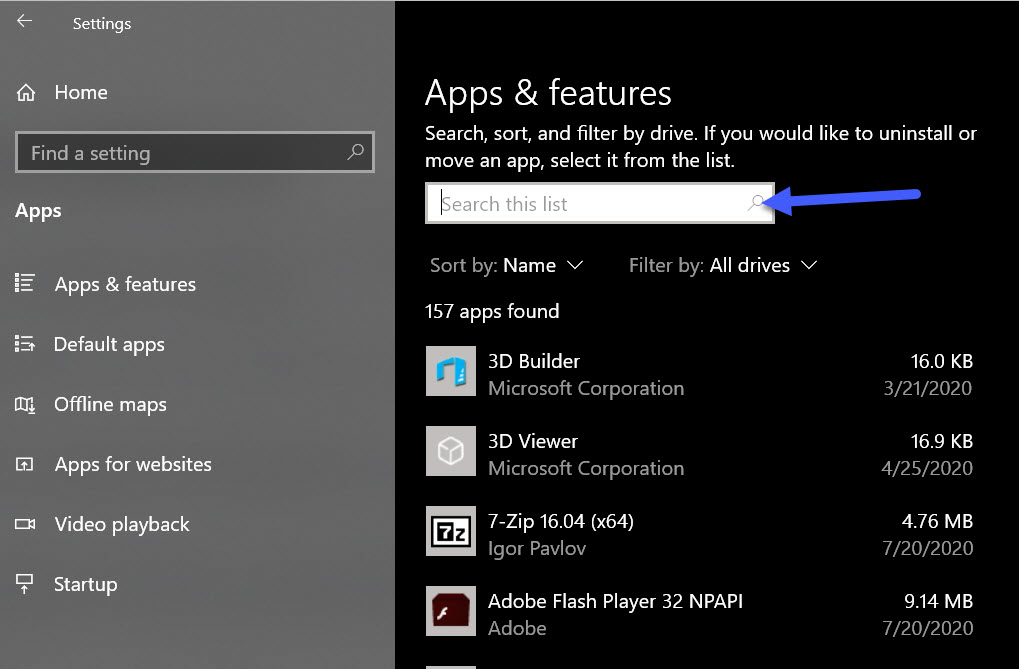
- Or the SettingSyncHost.exe was installed using the Windows Installer then to uninstall it Go to System Settings and open Add Or Remove Programs Option.
- Then Search for SettingSyncHost.exe or the software name Microsoft Windows Operating System in the search bar or try out the developer name Microsoft Windows Operating System.
- Then click on it and select the Uninstall Program option to remove SettingSyncHost.exe file from your computer. Now the software Microsoft Windows Operating System program along with the file SettingSyncHost.exe will be removed from your computer.
Frequently Asked Questions
How do I stop SettingSyncHost.exe process?
In order to stop the settingsynchost.exe process from running you either have to uninstall the program associated with the file or if it’s a virus or malware, remove it using a Malware and Virus removal tool.
Is SettingSyncHost.exe a Virus or Malware?
As per the information we have the SettingSyncHost.exe is not a Virus. But a good file might be infected with malware or a virus to disguise itself.
Is SettingSyncHost.exe causing High Disk Usage?
You can find this by opening the Task Manager application (Right-click on Windows Taskbar and choose Task Manager) and clicking on the Disk option at the top to sort and find out the disk usage of SettingSyncHost.exe.
Is SettingSyncHost.exe causing High CPU Usage?
You can find this by opening the Task Manager application and finding the SettingSyncHost process and checking the CPU usage percentage.
How to check GPU Usage of SettingSyncHost.exe?
To check SettingSyncHost.exe GPU usage. Open the Task Manager window and look for the SettingSyncHost.exe process in the name column and check the GPU usage column.
I hope you were able to learn more about the SettingSyncHost.exe file and how to remove it. Also, share this article on social media if you find it helpful.
Let us know in the comments below if you face any other SettingSyncHost.exe related issues.

He is the founder of howtodoninja.com and is an experienced tech writer and a cybersecurity enthusiast with a passion for exploring the latest technological advancements. He has 10 years of experience in writing comprehensive how-to guides, tutorials, and reviews on software, hardware, and internet services. With an interest in computer security, he strives to educate users by writing content on how to use technology, and how to also protect their smart devices and personal data from cyber threats. He currently uses a Windows computer, and a Macbook Pro, and tests hundreds of Android phones for writing his reviews and guides.

